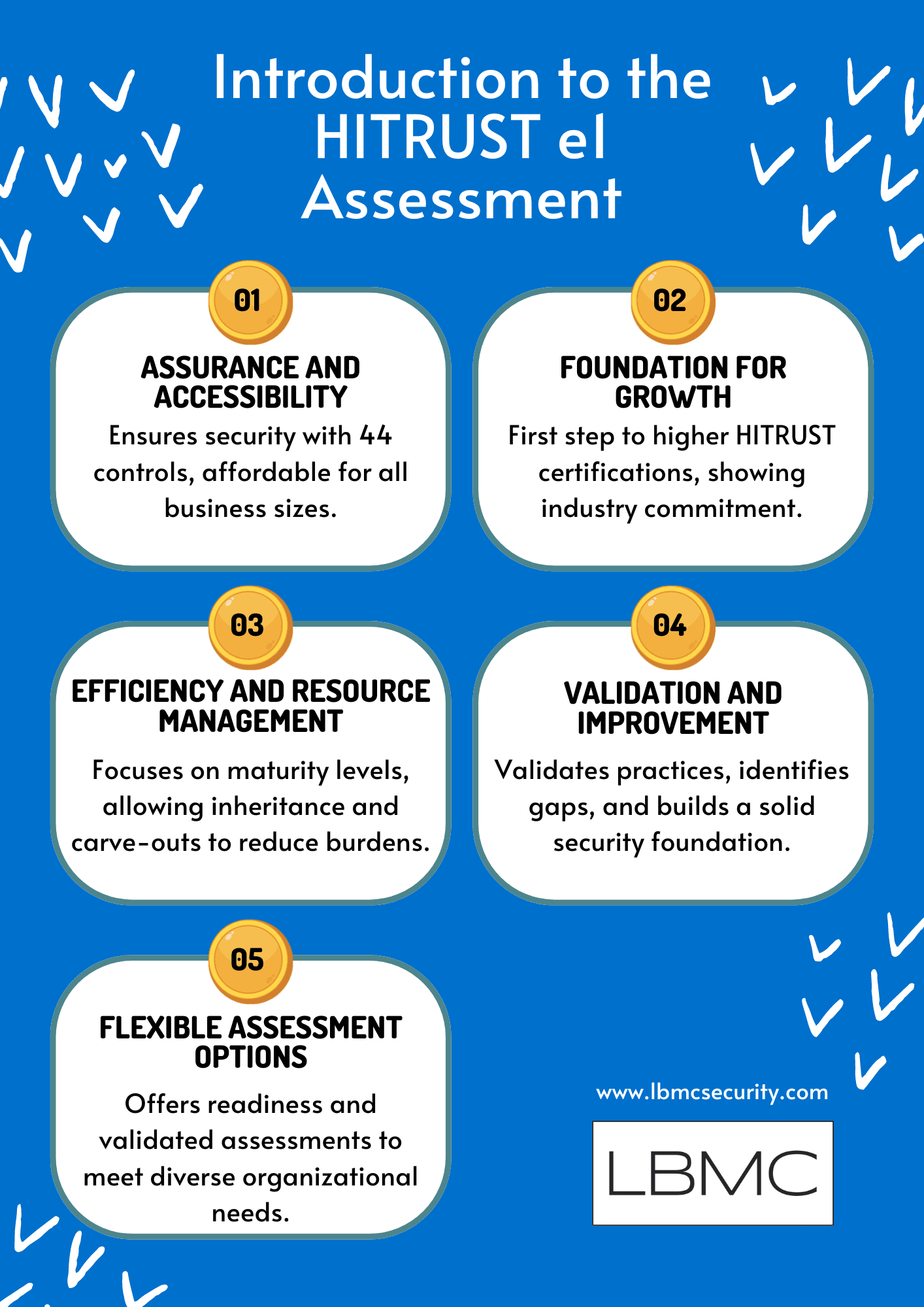
Key Takeaways:
- Assurance and Accessibility: With 44 critical controls, the HITRUST e1 evaluation guarantees information security and is economically priced and easily available for any kind of company.
- Foundation for Growth: Presenting industry standards, the e1 exam is a first step toward higher-level HITRUST certifications.
- Efficiency and Resource Management: It emphasizes on applied maturity levels and lets inheritance and carve-out strategies, so lowering assessment loads and besting resource allocation.
- Validation and Improvement: The e1 guarantees dependability and efficiency by verifying security processes, spotting flaws, and so strengthening a strong security basis.
- Flexible Assessment Options: Offering Readiness and validated exams, flexible assessment options help to meet different company demands for certification and cybersecurity improvement.
Introducing the HITRUST e1 Assessment
The HITRUST e1 evaluation offers confidence on the information security policies your company follows. It also lets one access the advantages of being an HITRUST certified company. Focused on 44 important cybersecurity controls, the HITRUST e1 assessment is an entry-level, 1-year evaluation. Designed to examine fundamental cybersecurity hygiene, the e1 evaluation offers companies of all kinds consistent information security assurance.
Is the e1 assessment the right fit?
In today’s competitive landscape, businesses of all sizes face the challenge of standing out in the marketplace. Whether you’re a nimble start-up or an established mid-size to larger firm, information security assurance is critical. Ensuring information security is key to building trust with your clients and stakeholders.
Accessible Assurance
For small businesses and start-ups, the e1 offers an accessible, lower cost security assessment. The e1 recognizes that small businesses operate on lean budgets and offers a streamlined process that doesn’t break the bank. From vulnerability scans to risk assessments, this assessment ensures your foundational security practices are robust. You get the essential security insights without unnecessary frills, allowing you to allocate resources wisely.
Stepping Stone to HITRUST
Larger firms seeking their first foothold in HITRUST assessments can also rely on the e1. Our comprehensive approach guides you through the process, demonstrating your commitment to industry standards. Choosing the e1 assessment is a strategic choice for organizations that need additional time to enhance their control environment. As you progress toward higher-level assessments, the e1 serves as a milestone, reflecting your commitment to securing sensitive data and continuous improvement.
Reliability and Effectiveness
The e1 doesn’t just provide a checkbox; it’s a guided journey that delivers reliable information security assurance. The e1 digs deep to validate your foundational security practices. Our experts validate your controls and identify gaps, thereby empowering you to build a solid security foundation—one that grows with your business.
The e1 serves as a reliable partner for businesses seeking information security assurance, making it a valuable asset in today’s competitive landscape. Regardless of your organization’s size, the e1 can ensure the reliability and effectiveness of your foundational security practices.
What are the benefits of the e1?
By zeroing in on the HITRUST implemented maturity level and allowing for both inheritance and carve out methods, the e1 reduces the assessment burden for your organization.
Implemented Maturity Focus
Unlike the more comprehensive r2 assessment, the e1 doesn’t segregate policies and procedures for separate testing and scoring; it instead integrates them into the overall evaluation. The e1 focuses on how well your organization has put security practices into action, testing one of the five HITRUST maturity levels, implementation. This approach is particularly valuable for businesses seeking a foundational understanding of their security posture.
While the e1 simplifies the assessment, it’s still essential to recognize that policies and procedures matter. They provide the framework for effective security practices. So, even though they aren’t scored independently, their alignment with implemented controls contributes to your overall security posture.
Inheritance and carve outs
Additionally, the e1 assessment offers the opportunity for both inheritance or the Carve-Out Method. Inheritance lets your company use security policies and procedures already in place elsewhere. Should your MSP or a partner company go through HITRUST evaluations, you can inherit their verified controls to expedites your assessment process. You build on the foundation others have laid instead of beginning from nothing.
If your organization relies on external vendors or partners for critical services (such as cloud hosting, payment processing, or data storage) and these third parties are not HITRUST certified themselves, the carve-out method is available. With carve-outs, you can isolate specific components of your environment that fall under third-party responsibility. These components are excluded from your assessment scope.
Carve-outs allow you to maintain e1 certification while acknowledging that certain aspects are handled externally. It’s a pragmatic approach that balances security and operational realities. For organizations collaborating with MSPs or relying on third-party services, these mechanisms reduce the burden of duplicative assessments. You can focus on what’s truly within your control while benefiting from existing security efforts.
Level of Effort and Resources
Compared to its more rigorous counterparts, the HITRUST i1 and r2 Assessments, the e1 assessment requires less effort to complete. It’s an easily available starting point for companies of all kinds since it balances offering significant assurance with reducing resource burden.
Based on our industry expertise, we compare the degree of lift to be roughly equivalent to a SOC 2 exam; e1 Readiness is most like a SOC 2 Type 1 and the full Validated assessment is most like a SOC 2 Type 2.
All in all, the HITRUST e1 Assessment empowers businesses by simplifying security evaluation, accommodating external partnerships, and optimizing resource allocation.
What service offerings are available for the e1?
Let’s review the HITRUST e1 Assessment options offered for organizations embarking on their HITRUST certification journey.
Readiness Assessment
The readiness assessment serves as the starting point for any organization venturing into HITRUST. It provides assurance that your existing security practices align with HITRUST’s stringent standards or are actively being remediated to meet those standards. Before committing to a full validated assessment, the readiness assessment allows you to assess your security posture without taking the financial risk associated with a comprehensive audit. We help you evaluate your practices against HITRUST’s requirements, identifying gaps and areas for improvement.
Validated Assessment
The validated assessment is the next step—an in-depth evaluation that goes beyond readiness. This is the full certifiable HITRUST assessment. Completion of the Validated assessment will provide assurance to any clients or stakeholders that your organization is adhering to foundational industry standard security best practices.
Traversable
All the work invested in the e1 assessment contributes to larger assessments like the i1 or r2. This alignment ensures that your efforts are not wasted and paves the way for future cybersecurity milestones. This is especially helpful if you are working with an organization in the healthcare industry that requires e1 certification road mapping to larger assessments by a certain time period.
Getting Started with LBMC’s HITRUST e1 Assessment
We recommend beginning with the readiness assessment. A readiness assessment is a prudent step to validate your practices before committing to a full assessment. By ensuring your security practices meet HITRUST standards early on, you mitigate the financial risk associated with a validated assessment. Think of readiness as the stepping stone—a way to gauge readiness and build confidence before diving into the full audit.
Don’t settle for mediocrity. Embrace the HITRUST e1 assessment and fortify your security foundation. Remember, your commitment to security speaks volumes.
Let LBMC help amplify your voice and guide you toward enhanced cybersecurity resilience through the HITRUST e1 assessment. Contact our HITRUST experts to get started.

